Bismilllahirrahmaanirrahim
(If you’re viewing this in your email inbox, please click here to visit the site. The email clips the article.Also, reading it on the desktop/desptop site version would give a much better reading experience. )
This is the biography of Edward Snowden.
Snowden used to work as a spy for the Central Intelligence Agency and National Security Agency but now, he works for the people. His career in American intelligence agency lasted a short seven years during which he saw the change from targeted surveillance of individuals to the mass surveillance of entire populations. He helped make it technologically feasible for a single government to collect all the world’s digital communications, store them for ages and search through them at will. Post 9/11, the IC was racked with guilt for failing to protect America. They sought to build a system that would prevent them from being caught off guard ever again and it’s foundation was to be technology. At the age of 22, Snowden got his first top secret clearance from NSA and less than a year later he was at the CIA as a systems engineer with sprawling access to some of the most sensitive networks on the planet. From 2007 to 2009 he was stationed at the US embassy in Geneva as one of the rare technologists deployed under diplomatic cover tasked with bringing the CIA into future, by bringing its European stations online, digitizing and automating the network by which the US government spied. By the age of 26 he was a nominal employee of Dell but again working for National Security Agency. He helped design what amounted to the agency’s global backup: massive covert network that ensured that even if the NSA’s headquarters were reduced to ash in a nuclear blast, no data would ever be lost. He came back to the United States at the age of 28 and received a promotion to the technical liaison team handling Dell’s relationship with the CIA. His team help the agency build a new type of computing architecture, “a cloud”, the first technology that enabled every agent no matter where they were physically located to access any data they needed, no matter the distance. He took up a new contract with the NSA at the age of 29 in Hawaii where he realized how he had helped in developing a giant machine to form a system of global mass surveillance. Deep in a tunnel in Hawaii he sat at a terminal which had practically unlimited access to the communications of every man, woman and child on earth who had ever dialed a phone or touched a computer.The reason we have this book is that Edward Snowden decided to tell the truth. He collected archived documents that gave evidence of the US government’s lawbreaking and turned them over to journalists.
Snowden says that the Internet of today is unrecognizable from the Internet of his childhood. He says that this change has been a conscious choice; the result of a systematic effort on the part of a privileged few. The internet turned commerce into e-commerce after companies realized that people who went online were far less interested in spending, than in sharing, and that the human connection the Internet made possible could be monetized. Then all companies had to do was figure out how to put themselves in the middle of those social exchanges and turn them into profit.This was the beginning of surveillance capitalism . Then it was the creative web that collapsed. The promise of convenience led people to exchange their personal sites for a Facebook page and a Gmail account. The successors to the e-commerce companies that had failed because they couldn’t find anything the consumers were interested in buying now had a new product to sell. That new product was ‘us’. Everything about Internet users came under surveillance and the surveillance would go on to be actively encouraged and even funded by an army of governments greedy for the vast volume of intelligence they would gain. The power of mass surveillance afflicts the innocent far more than the guilty. Snowden says that it has been six years since he came forward and he has witnessed a decline in the commitment of advanced governments throughout the world towards protecting the privacy of their citizens .This decline has only continued as democracies regress into authoritarian populism. Nowhere has this regression been more apparent than in the relationship of governments to the press. The same agencies that over the span of Snowden’s career had manipulated intelligence to create a pretext for war, used illegal policies, and a shadow judiciary to permit kidnapping as extraordinary rendition, torture as enhanced interrogation, and mass surveillance as “bulk collection”, didn’t hesitate for a moment to call him a Chinese double agent, a Russian triple agent and worse,a “millennial”. Edward Snowden did not disclose a single document directly to the public. He disclosed the government’s documents only to the journalists because he refuses to presume himself to be the sole arbiter of another’s privacy. This is an account of his life.
Part one:
Snowden says the first thing he ever hacked was bedtime when he was six years old. He went about covertly resetting all the clocks in the house by several hours. But how would you do it now in the age of Internet. Look at your phone, you’ll see that time on your phone is automatically set.Every so often your phone quietly asks your service providers network, “hey do you have the time?”. That network in turn asks a bigger network which asks an even bigger network and so on through a great succession of networks, until the request reaches the true Masters of times, are at work: times server run or referenced against the atomic clocks kept at places like the National Institute of Standards and Technology in the United States or Institute of Meteorology and Climatology in Switzerland and the National Institute of Information and Communications Technology in Japan. That long invisible journey accomplished in a fraction of a second.
Snowden was born in 1983. And that was the year that the US Department of Defense split its internal system of interconnected computers in half, creating one network for the use of the defense establishment called MILNET and another network for the public, called the Internet. New rules defined the boundaries of the virtual space giving rise to the Domain Name System that we use today: the .gov, .mil, .edus and .com,and the country codes assigned to the rest of the world like .uk, .de, .fr, .cn, .ru. It would be another six years before the World Wide Web would be invented.
The Internet is not a single entity. It is a global cluster of interconnected communications network that 3 billion people or roughly 42% of the world’s population use regularly. In a broad sense it means the universal network of networks connecting the majority of the world’s computer to one another by a set of shared protocols. Now what are protocols? Think of protocols as languages for machines, the common rules they must follow. For example HTTP refers to Hypertext Transfer Protocol, the language used to access the World Wide Web. Every time we check our email we use a language like IMP (Internet message access protocol), SMTP (simple Mail transfer protocol), POP3 (post office protocol).All these protocols are known as application protocols . In order for the data in any of these application protocols to cross the Internet and be delivered to your device, it first has to be packaged up inside a dedicated transport protocol; think of how the regular Postal Service prefers you to send your letters and parcels in their standard size envelopes and boxes. Similarly, protocols just standardize the format in which data is passed to and fro. These protocols have given us the means to digitize and put online damn near everything in the world.
Snowden recalls his childhood and the first 9 Internet-less years of his life. He would spy on his older sister Jessica and he would spy on his mother Wendy but most of all he spied on his father who was a Coast Guard. His father left home early and came home late often with new gadgets. One day his father father brought home a computer system and some video games. That was one of the first interaction of Edward Snowden with technology.
His mother loved giving him maths challenges. She would have him pick out books and model cars at malls and buy them for him if he was able to mentally add together their prices. On Christmas 1989, a nintendo appeared in his house but a rule was imposed that he could only rent a new game when he finished reading a book. One day his Super Mario Bros cartridge wasn’t loading and Snowden decided to fix it himself. He was just seven years old and he went on to dismantle the entire console with a screwdriver. After wiping and blowing on the circuit board, he tried to reassemble it; he somehow pushed the lid close but the console refused to work. When his father returned home, surprisingly, he was not angry, and patiently explained that in order to fix a malfunction one had to analyze the mechanism of individual parts of a machine. . You must know how the device you’re handling works. This was a lesson in self reliance for Snowden. He believes that the lack of understanding of this fact alone virtually guaranteed technological tyranny which was perpetrated not by technology itself but by the ignorance of everyone who uses it daily and yet fails to understand it. To refuse to inform yourself about the basic operation and maintenance of the equipment you depended on was to passively agree to its terms, when your equipment works you’ll work and when your equipment breaks down you’ll breakdown too.
Snowden’s father decided he was ready to see his lab. The lab was dim and empty and it was filled with several screens of computers. His father showed them to him one by one and tried to explain how they worked. He found himself in front of a keyboard. His father told him that every key on the keyboard had a purpose and opened a text editor and wrote down a couple of lines on a paper nearby for Snowden to type it on the keyboard. It was a simple code which asked the user for his name and allowed the user to input some characters. He was fascinated, and this was his introduction to programming and to computing in general. These machines do what they do because somebody tells them to in a very special, very careful way. Nowhere else had he ever felt so much in control.
Snowden’s family moved to Maryland when he was barely 9. Suddenly he found himself in a school where he felt alienated and constantly mocked for his glasses, disinterest in sports and specially his accent. He got so sensitive about his accent that he completely stopped talking add his grades plummeted. His father worked as a chief Warrant Officer in the aeronautical engineering division at Coast Guard headquarters. His mother worked at Fort Meade. He stresses that this kind of employment was normal. Everyone they knew worked for the government either it was the Department or Department of Energy or Department of Commerce or the FBI. The place was home to 115 government agencies in addition to forces from all the five branches of the military. To put it in perspective, in Anne Arundel County, in a population of just over half a million, every 800th person works for the post office, every 30th person works for the public school system and every fourth person works for or serves in a business agency or branch connected to Fort meade. Both his parents had top secret clearances. His mother worked as a clerk at an independent insurance and benefits Association that served employees of the National Security Agency. His father’s career remained fairly opaque to him. Nobody really talked about their jobs. Most of them are legally prohibited from discussing their work even with their families . Snowden also stresses that tech-people rarely ever have a sense of the product applications and policy implications of the projects to which they are assigned. They are never told the larger project for which their skills are going to be used.
His family soon got their first desktop computer, a Compaq Presario 425. The computer became his constant companion. He was barely short of being addicted to the machine. He tried to rush his family through their tasks so he could get back to his which were more important like playing video games. There for him was the true magic with just one cord, the computers expansion card and modem and a working phone he could dial up and connect to something new called the Internet. It was a miracle for him. Internet access and the emergence of web was his generation’s Big Bang, it became his sanctuary. He stopped sleeping at night and his grades went back into freefall, after all the education that he was getting online seemed better and even more practical then what he received at school. He developed an insatiable curiosity about nearly everything he heard of. A crash course on how to build his own computer led to a crash course in processor architecture with side excursions into information about martial arts, guns ,sports car and and goth porn. He’d stay up all night and browse the web hiding from his parents. It was the era before the online world became centralized and consolidated by governments and businesses. To this day he considers the 1990s online to have been the most pleasant and successful anarchy he has ever experienced. The strangers on the Internet were so considerate and thorough that would be unthinkable today. When he panicked about a query on a certain chipset, a professional computer scientist on other side of the country or wrote a 2000 word explanation to help him solve it. One of the greatest joys of their Internet was anonymity. And the ability to to delete your previous mistakes. His computer skills were improving so swiftly that instead of being proud of all the progress he had made , he was embarrassed by his previous ignorance and would go away and delete all his previous history on the Internet. Mistakes that were swiftly punished but swiftly rectified allowed both the community and the offender to move on. To him this felt like freedom. Internet dissociative opportunities actually encouraged him and those of his generation to change their most deeply held opinions instead of just digging in and defending them when challenged.
As he turned 13 years old, he vowed to never return or to take seriously his classroom commitments. He analysing the exam marking pattern to understand how he could score enough to pass his classes yet still not have to attend every single class and finish every single assignment. He would use his free time to browse the web. Unshackled from homework he started doing some more conventional computer based hacking and his abilities improved gradually. Once he was reading some article about the history of American nuclear program and before he knew it, he was at the website of Los Alamos National Laboratory, the country’s nuclear research facility. He noticed a glaring security hole in their website which was an open directory structure. Imagine you get sent a link to download a PDF file that’s kept on a multipage website. Most websites will confine your visit to that specific file keeping their entire directory or library closed and private. But back in those days even major websites were created and run by folks who are new to technology and they often left their entire directory or library wide open which meant that if you truncated the website’s URL, you would be able to access every file on their site, PDF or otherwise, including those that weren’t necessarily meant for visitors. He had stumbled upon a trove of files meant only for the lab security workers. He sent an explanatory mail to the laboratory’s Webmaster about the vulnerability and waited for a response that never came. He regularly checked the website to see if they had fixed it but there are been no change, when one day, after several weeks the phone rang during dinner time. His mother picked a phone and all color drained out of her face as she handed the phone to Snowden. On the line was a friendly representative from Los Alamos IT who thanked him for reporting the problem and Snowden calmly explained how he had found the directory traversal problem, how he reported it etc While hanging up the officer asked him to keep his contact and get in touch with him when he turned 18.
Snowden never took school seriously and the constant reproach of the administration never bothered him. However at the end of his freshman year he was faced with a different kind of assignment which was to produce an autobiographical statement of no fewer than 1000 words. He did not know what to write. His parents were getting a divorce and he reacted by turning inwards. When he was alone he was subdued even morose,he constantly worried about being a burden he started ignoring his emotions, and feeling of self sufficiency. He started calling himself Ed. At the beginning of the sophomore year he started getting tired a lot and falling asleep more than usual not just at school anymore but now even at the computer. Soon his joints were aching his nodes were swollen and the whites of his eyes turned yellow. He was diagnosed with infectious mononucleosis. School was totally forgotten and his absences piled up. He wondered why he was even alive and just at the point when his glandular disease had developed into full on depression the school informed him that he needed to repeat two semesters. Suddenly he was back online and on the phone searching for systems edges, searching for a hack. After a bit of research he realized that apparently you don’t need a high school diploma to apply to colleges. After a lot of form filling he got himself accepted to a college, Anne Arundel Community College. He was the youngest person in his class. He figured out that by taking classes above his grade level he wouldn’t have to suffer through the year he had missed. He just skipped it. By the age of 16 he was pretty much living on his own. He met a new friend group in Japanese class where he met an older woman called Mae. She was his Japanese conversation partner and also ran a successful web design business call Squirreling Industries. He soon became a freelancer and started working as a web designer for her. He thought that he was in love with her and would do everything she asked him to even though she was married and never led him on. Her house was located on base at the southwestern edge of Fort Meade where her husband worked as an Air Force linguist assigned to the National Security Agency. It’s nearly inconceivable now but at that time Fort Meade was almost entirely accessible to anyone. About a year into his tenure with squirreling industries he realized he had to plan for his future. Professional industry certifications for the IT sector were becoming hard to ignore. The certification credentials were being adopted as industry standard almost as quickly as the industry could invent them. With payments looming on his tuition loan he asked Mae to give him more work so he could earn more. She agreed and asked him to start coming in at 9:00 AM.
On September 11 as he sat at Mae’s home, she received a call and immediately turned on the television. There was the news about a plane hitting one of the twin towers of the World Trade Center. A second plane just hit the other tower. The Pentagon was attacked then. Madness poured out of agencies black glass towers . NSA director Michael Hayden issued the order to evacuate before most of the country even knew what had happened. Snowden got into his car and tried to drive home as well. In the ensuing days and weeks, the NSA’s special police were joined by convoys of Humvees top with machine guns guarding the roadblock and checkpoints. Many of these new security measures became permanent supplemented by endless rules of wires and massive installations of surveillance cameras. These trappings of what would be called the War on Terror were one of the reasons why he gave up on Mae after 9/11. By the time she and her husband moved to California she felt like a stranger to him. She was too opposed to the war and he couldn’t understand why.
Nearly 3000 people died on 9/11 and over 1 million people have been killed in the course of America’s response. The two decades since 9/11 have been a litany of American destruction with the promulgation of secret policies, secret laws, secret codes and secret wars. Snowden says that having spent roughly half that time as an employee of the American intelligence community, he knew better than most how often the agencies got things wrong. America had issued a new order which was of total submission:stop resisting. Whenever he tried to understand how the last two decades happened, he returns to that September, to that Ground Zero of 9/11’s immediate aftermath. To return to that fall means coming up against the truth darker than the lies that tied the Taliban to al Qaeda and conjured up Saddam Hussein’s illusory stockpile of weapons of mass destruction.
America immediately divided the world into “us” and “them” and everyone was either with us or against us as President Bush so memorably remarked. People in his neighborhood put up new American flags as if to show which side their chosen. He would sometimes got o shooting clubs and now next to shooting range old targets, the bull’s eyes and flat silhouettes were effigies of Middle eastern men in Arab headdress. Guns that had languished for years behind the dusty glass of display cases were now marked sold. Nearly 100,000 spies returned to work. Meanwhile their bosses got busy campaigning for extraordinary budgets and extraordinary powers leveraging the threat of terror to expand their capabilities. September 12 was the first day of a new era.
Snowden says that his country could have done so much with this opportunity and could have treated terror not as the theological phenomena it purported it to be but as the crime it was. It could have used this rare moment of solidarity to reinforce democratic values and cultivate resilience in the now connected global public. Instead, it went to war. He says that the greatest regret of his life is his reflexive unquestioning support for that decision. He was outraged and accepted all the claims retailed by the media as facts and embrace the truth constructed for the good of the state. At the time he was growing up, America lacked enemies. It was the sole global power. There were no new frontiers to conquer or great civic problems to solve except online. The attacks of 9/11 changed all that. Now finally there was a fight. A normal IT job seemed too comfortable for him now, he wanted to fight the enemies. Unfortunately the primary agencies that did that, the NSA and CIA, had their hiring requirements written ½ century ago and required a traditional college degree but the agencies were growing so much and needed technical assistance so desperately that they waived the degree requirement for military veterans. Snowden decided to join the army.
He joined the army and scored high enough on his entrance exam to qualify for a chance to come out of training as a special forces sergeant. He had to go through basic training at Fort Benning Georgia. The physical training completely drained him and once while he was on track scrambled atop a tree that arched over the path, he noticed a snake and lost his balance and fell down. He knew immediately something was wrong. He had bilateral tibial fractures. He was despondent if he didn’t finish the basic training cycle on time he would lose his slot which meant that he'd be reassigned according to the needs of the army. They could make him into whatever they wanted, a mechanic, a desk jockey, a potato peeler! The doctor offered him administrative separation which was only available to enlistees who had been in the services fewer than six months. He had to sign a statement attesting that he was all better and his bones were all healed. As he held the statement, a knowing smile crossed his face. He recognized the hack. The administrative separation was the government's way of avoiding liability and disability claim. Under the military’s rule if he had received a medical discharge the government would have had to pay the bills for any issues stemming from his injury and treatment and therapies it required. An administrative discharge put the burden on him and his freedom hinged on his willingness to accept that burden. He signed and left that same day.
He still had the urge to serve his country and if he couldn’t do it through his body then he would do it through his head, via computing . He understood the necessity for a security clearance if you wanted to work at the intelligence agency. There are three levels of security clearance from low to high, confidentials, secret and top secret. The last can be further extended with a sensitive compartment information qualifier creating the coveted TS/SCI access required by positions with top tier agencies CIA and NSA. He applied for the clearance of the same. He was a perfect candidate on paper. He was a kid from a service family and almost every adult member of his had some level of clearance. He had no criminal record and no drug habit.
This was the time Snowden also joined a dating site called “Hot or Not” where people rated each other based on their pictures and if each had rated the others photo hot, they were able to contact each other. This is how Edward Snowden met his life partner Lindsay Mills. She studied fine art photography and had her own website where she kept a journal. They soon met and found out that online spark had translated even in real life They confided in each other everything and he had never felt so comfortable around anyone.He had her thoughts in his head when he went to NASA’s friendship annex complex for the final interview for his security clearance. He was connected to a large polygraph machine and was asked generic questions about his life. He passed with flying colors which meant that not only had a qualified for the TS/SCI, he had also cleared the full scope polygraph, the highest clearance in the land. He was only 22 years old.
Part 2
At this point Edward Snowden explains about his politics at the age of 22. He didn’t have any. His parents were dismissive of politics in general and more dismissive of politicians. It was a certain bemused detachment particular to their class of federal civil servants or who can be referred to as the deep state or the shadow government. They are a class of career officials who unelected and non-appointed worked in the government either at one of the independent agencies like the CIA and NSA or at one of the executive departments like state Treasury, Defense, Justice and like. A nearly 3 million strong professional government workforce dedicated to assisting the amateurs chosen by the electorate and appointed by the elected in fulfilling their political duties. These civil servants stay in their positions even as administrations come and go work as diligently under Republicans as under Democrats because they ultimately work for the government itself. The patriotism taught by Snowden’s parents had easily converted into nationalist fervor. However as his abilities developed he realized that the technology of communications had a chance of succeeding where technology of violence had failed. Democracy could never be imposed at the point of a gun. The Internet was the freest society. A place where everyone was equal, a place dedicated to Life, Liberty and Pursuit of Happiness . An open frontier that belonged to anyone bold enough to settle in it. John Perry Barlow’s “Our Declaration of Independence of Cyberspace” stated, “We are creating a world that all may enter without privilege or prejudice accorded by race, econonmic power, military force or birth. We are creating a world where anyone anywhere may express his or hers believes no matter how singular without fear of being coerced into silence or conformity”.
There were different careers available to Snowden as a technologist working for the government. He chose to get into Systems which was like being an urban planner, to take all of the components available an ensure their interaction to maximum effect. There are two ways to be a systems guy. One is that you take position of the whole of an existing system and maintain it gradually making it more efficient in fixing it when it breaks. That position is called System Administrator or sysadmin. The second is that you analyze the problem such as how to store data or how to search across databases and solve it by engineering a solution from a combination of existing components or by inventing entirely new ones. This position is called systems engineer. Snowden came about to do both of these jobs. The job of technologist is often very specialized and they are kept detached from different departments. This is to ensure that no one person can have access to all sensitive information. Over the course of his career it became increasingly difficult for him to ask questions about the technologies he was responsible for. A number of times he could not figure out what the technology he was working at was being used for.
He had hoped to serve his country but instead he went to work for it. By the time he noticed it , working in the sincerity of public service had given way to greed of the private sector. America heavily relies on contracting with the help of privatized forces to keep the National Defense working. Today contracting is most often associated with its major failures such as fighting for hire work of Blackwater (which changed its name to XY services after its employees were convicted of killing 14 Iraqi civilians and then changed its name to Academi after it was acquired by a group of private investors), or the torture for hire work of CACI and Titan both of which supplied personnel who terrorized prisoners at Abu Ghraib. Contracting is essentially a process by which the Defense department of USA hires employees of private companies like Dell to work for them or handle their technology. So on paper the workers are employees of the private company but instead they report to the government. The primary purpose served by contracting is that it lets agencies avoid federal limit on hiring. Every agency has a head count that dictate the number of people it can hire to do a certain type of work. But contractors because they are not directly employed by the federal government aren’t included in that number. The agencies can hire as many of them as they can pay for and they can pay for as many of them as they want, all they have to do is testify to a few select congressional subcommittees that the terrorists are coming for our children or the Russians are in our emails or the Chinese are in our power grid. Congress never says no to this type of begging. Among the documents that Snowden provided to journalist was the 2013 Black Budget. This is a classified budget in which over 68% of its money around 52.6 billion dollars was dedicated to intelligence community including funding for one 207035 IC employees more than 1/5 of whom were full-time contractors. And that number doesn’t even include the 10s of thousands more employed by companies that have signed contracts or subcontracts or sub subcontracts with the agencies. These contractors are never counted by the government not even in the black budget because to add their ranks, the contracting total would make one disturbing fact extraordinary clear, the work of American intelligence is done as frequently by private employers as it is by government servers.
Snowden was officially an employee of the state of Maryland working for the University of Maryland at College Park. The University was helping the NSA open a new institution called CSL the Center for Advanced Study of Language. The mission of the center was to study how people learn languages and to develop computer assisted methods to help them do so more quickly and better. The NSA was having a tough time ensuring that its computers could comprehend and analyze the massive amount of foreign language communication that they were intercepting or spying upon. His responsibilities included showing up everyday to patrol the empty halls after the construction workers had left and make sure nobody broke in or bugged in at night. During daytime he caught up on his sleep and went out with his girlfriend Lindsay Mills.
After the 2013 revelations by Snowden, the US government tried to disparage him by referring to him as only a contractor or a former employee with the implication that he didn’t enjoy the same kinds of clearance and access a blue badged agency staff. In national security contracting especially in tech contracting, you often find yourself physically working at an agency facility but nominally on paper working for Dell or Lockheed or Martin or other private companies.
His first major contractor gig was actually a subcontracting gig. The CIA had hired BAE systems which had hired COMSO which hired him. With a salary of $62,000 per year, he never once worked at the COMSO office. He took orders directly from the CIA and had to move to Virginia. He reported every day at the new headquarters building of the CIA with other young techies all of whom wore contractor badges. There is a remarkable similarity between the intelligence community and the tech industry; both are entrenched in unelected powers that pride themselves on maintaining absolute secrecy about their developments. Nothing inspires arrogance like a lifetime spent controlling machines that are incapable of criticism. Both believe that they have the solutions for everything which they never hesitate to unilaterally impose. Above all they both believe that these solutions are inherently apolitical because there based on data whose decisions are regarded as preferable to the chaotic whims of the common citizen.
At the end of the indoctrination program of the newly recruited techies, suddenly the lights came down in the room and the power point was wired up and faces appeared on the screen that was bolted to the wall. These were the faces of former agents and contractors who whether through greed,malice, incompetence or negligence failed to follow the rules. The people on the screen, it was implied, were now in basements even worse than this one and some would be there until they died. It is said that ever since Snowden’s career ended, this “Parade of Horribles” of incompetents moles, defectors and traitors has been expanded to include an additional category: people of principle, whistleblowers in the public interest. Snowden hopes that the next 20 something group of techies are struck by the governments conflation of selling secrets to the enemy and disclosing them to journalists when the new faces, when his face, pops up on the screen.
Snowden’s team was attached to the directory of support and his task was to manage the CIA’s Washington Metropolitan server architecture. His top security clearance reflected him having been a read into a few different compartments of information. Some of these compartments were SIGINT (signal intelligence) and another was HUMINT (human intelligence). On top of these he was read into COMSEC (communication security) compartments that allowed him to work with cryptographic key material, the codes that are used to protect all other agencies secret. The cryptographic material was processed and stored on the servers he was responsible for managing.
In the CIA, secure offices are called vaults and his team’s vault was located a bit past the CIA helpdesk station. His job was to sit in the secure office 12 hours each night and keep the CIA’s global network online. Was something to go wrong he had to log in to try to fix it remotely. One of his seniors who also work the night duty was given the task of backing up the data every few hours into a tape. He said that the CIA did not trust their own servers as they are always breaking. But when the servers breakdown, they risk losing whatever they were storing so in order not to lose anything that comes in during the day, they back up everything on tape at night. The old way. Tape hardly ever crashes.
When you go online at the CIA you have to check a box or consent to monitoring agreement which basically says that everything you do is being recorded. This is one major reason why most IC workers don’t share civilian customers’ concern about being tracked online, because they have simply become desensitized to being tracked all the time. The CIA has its own Internet and web. It has its own kind of Facebook which allows agents to interact socially, its own type of Wikipedia which provides agents with information about agency teams projects and missions and its own internal version of Google, actually provided by Google, which allows agents to search this sprawling classified network.
The disorganised CIA quite understands that the computer guy knows everything or rather can know everything. The essence is that the more system levels privilege he has, the more access he has to virtually every bit of CIA’s existence. Among the things Snowden Googled on CIA server out of curiosity and fun, were: aliens have never contacted the earth, climate change is real, man really did land on moon, chemtrails are not a thing, and al Qaeda maintained close ties with Saudi a fact that the Bush White House works suspiciously hard to suppress. The CIA’s internal news sites had top secret dispatches regarding trade talks and coups as they were still unfolding. He was so fascinated by how truly international the CIA was that he decided to give up his job as a private contractor to CIA and instead work directly under the government. This would mean that as a government employee would be paid lesser than a private employee but then he would have much more opportunities to travel. He applied for a systems administrator at the CIA and was accepted. But before going back to work he had to finish a sit in a classroom schooling to get prepared.
He was sent to Warrenton training center in Virginia and a place called Comfort Inn was to be his home for the next six months. Warrenton was nicknamed The Hill and is believed to be the most mysterious and classified center of CIA. The Hill served as the heart of CIA’s field communications network. Being trained to be a TISO (Technical Informant Security Officers) that is, the CIA’s cadre of elite communicators. A TISO is an undercover officer to manage the technical infrastructure of CIA operations most commonly overseas at stations hidden inside American missions consulates and embassies. They are responsible for knowing how to fix basically every machine in the building. If an embassy is under siege, the TISOs are always the last guys out. It’s their job to send the final “off the air” message to headquarters after they have shattered, burnt, wiped and disintegrated anything that the CIA has its fingerprints on. The worst kept secret in modern diplomacy is that primary function of an embassy nowadays is to serve as the platform for espionage. Only espionage justifies the expense for the ability of a country to use the cover of its foreign services to conduct and legitimize its spying.
Snowden was assigned to work in Geneva.
In the intelligence community, the Frankenstein Effect refers to situations in which policy decisions intended to advance American interests that end up harming them irreparably. Some examples include American funding and training of mujahideen to fight the Soviets which resulted in the radicalization of Osama bin Laden and the founding of al Qaeda as well as de-bath-ification of the Saddam Hussein era Iraqi military which resulted in the rise of Islamic state. In Geneva , America was busy creating a network that would eventually take on a life and mission of its own and wreck havoc on the life of his creator. The CIA traditionally handed its intelligence with the help of human intelligence or covert officers who specialized in face to face information collection. As everything was being digitized Geneva was regarded as the Ground Zero for this transition because it contains the world’s richest environment; sophisticated targets from the global headquarters of United Nations to the home offices of numerous specialized UN agencies and international nongovernmental organizations. Intelligence was increasingly becoming cyber-intelligence and anyone could be searched while the searcher would remain anonymous. An issue would emerge when a case officer would search the name of a person from a country like Iran or China in the agencies databases and come up empty handed. They turned to the public Internet which was risky. When you go online you request for any website travels from your computer to the server that hosts your final destination that is the website you’re trying to visit. At every stop along the way however you request announces exactly where on the Internet it came from an exactly where an Internet is going thanks to identifiers called source and destination headers, which you can think of as the address information on a postcard. Because of these headers, your Internet browsing can easily be identified as yours by webmasters’ network administrations and foreign intelligence services..
During his stay in Geneva, whenever a case officer asked him if there was a safer, faster and all around more efficient way to do this he introduced them to Tor. The Tor project was the creation of the State that ended up becoming one of the few effective shields against their state surveillance. Tor is a free and open source software that allows users to browse online with the closest thing to perfect anonymity. Its protocols were developed in the US naval research laboratory throughout the mid 1990s and in 2003 it was released to the public, to the world wide civilian population on whom its functionality depends. Tor operates on a cooperative community model relying on tech savvy volunteers all over the globe who run their own Tor servers out of their basements, attics and garages. Tor does the job of protecting the origin of the Internet traffic . With Tor protocol, your traffic is distributed and bounced around through randomly generated pathways from Tor server to Tor server with the purpose being to replace your identity as the source of a communication with that of the last or server in the constantly shifting chain. Virtually none of the Tor servers know the identity of the origin of the traffic. Tor server that does know the origin is the very first server in the chain but it does not know whether traffic is headed. This layering method is called The Onion Routing which gives TOR its name. The classified joke was that trying to surveil the Tor network makes spies want to cry. Therein lies the project’s irony, here was a US military developed technology that made cyber intelligence simultaneously harder and easier applying hacker know-how to protect the anonymity of IC officers but only at the price of granting the same anonymity to adversaries and to average users across the globe.
The Internet is fundamentally American. The World Wide Web might have been invented in Geneva at the CERN research laboratory in 1989 but the ways by which the web is accessed are American; which gives the American intelligence community the home field advantage. The cables and satellites, the servers and towers, so much of the infrastructure of the Internet is under the US control that over 90% of the world’s Internet traffic passes through technologies developed, owned and operated by American government and American businesses. Countries like China and Russia have attempted to make alternative systems such as the Great Firewall or state sponsored, censored search engines or the nationalized satellite constellations that provide selective GPS but America remains the hegemon. It’s not just in terms of infrastructure, but it’s also the computer software, from Microsoft, Google to Oracle and hardware from HP, Apple and Dell, everything from chips (Intel, Qualcomm) to the routers and modems (Cisco or Juniper) to the web services and platforms that provide email and social networking and cloud storage (Google, Facebook) and the more structurally important Amazon which provides cloud services to the US government along with half the Internet. Though some of these companies might manufacture their devices, say in China, the companies themselves are American and subject to American law. The problem is that they are also subject to classified American policies that pervert law and permit the US government to surveil virtually every man, woman and child who has ever touched a computer or picked up a phone. Given the American nature of communication infrastructure it should have been obvious that the US government would engage in this type of mass surveillance.
Snowden moved to Japan in 2009 to work for the NSA America’s Premier Signals Intelligence Agency. Again working as a private contractor he became an employee of Dell formally but only ever worked in an NSA facility. The NSA’s Pacific Technical Center (PTC ) occupied ½ of a building inside the enormous Yukuto air base. The PTC handled the NSA’s infrastructure for the entire Pacific and provided support for agency’s spoke sites in nearby countries. Communications interception was a major part of the mission. Snowden’s job was systems analysis with responsibility for maintaining the local NSA system and connecting it with the structure of CIA. The NSA was much more technologically sophisticated compared to the CIA but much less vigilant about its security. Each of any CIA’s site collected its own intelligence, stored the data on its own local service and often then sent back copies to the main servers at NSA headquarters. This meant that if any data were destroyed at any particular site then the intelligence that the agency had worked hard to collect would be lost. This problem was acknowledged and Snowden was given the task of engineering a solution. The result was a backup and storage system that would act as a shadow, a complete automated and constantly updating copy of all the agency’s most important material. The NSA’s conventional wisdom was that there was no point in collecting anything unless they could store it until it was useful, and there was no way to predict when exactly that would be. The agency’s ultimate dream was permanency; to store all the files it has ever collected till perpetuity.The NSA had developed several programs meant for spying, like FOXACID which was the code name for NSA servers that host malware versions of familiar websites. EGOSTISTICALGIRAFFE was an NSA program intended to exploit a vulnerability in certain web browsers running Tor since they couldn’t break Tor itself. GRAPHICTHIEF was the VPN attack orchestrator.
In the midst of work, Snowden was informed that the PTC hosted a conference on China sponsored by the Joint Counterintelligence Training Academy where he was asked to be the technology briefer. He prepared his presentation on counterintelligence, cyber intelligence and ways to thwart the adversary’s attempt to use the Internet to gather surveillance. The primary task was to provide a summary of the intelligence community’s assessment of China’s ability to electronically track American officers and assets operating in the region. On reading the technical details of China surveillance of private communications, Snowden was completely appalled as well as impressed. But there were certain aspects of what he was reading that disturbed him. There was simply no way for America to have so much information about what the Chinese were doing without having done some of the very same things itself. What China was doing publicly to its own citizens, America might be doing secretly to the whole world.
After 9/11 president George W Bush lead one of the most publicly contested initiative of ,mass surveillance which was the warrantless wiretapping component of the President Surveillance Program (PSP) which had been disclosed by the New York Times in 2005 by some whistleblowers. The PSP empowered the NSA to collect telephone and Internet communications between the United States and abroad without having to obtain a special warrant from a foreign intelligence surveillance court. Following the outcry that attended the Times revelations, the Bush administration claimed to have let the program expire in 2007. But the expiration turned out to be a farce. Congress spent the last two years of the Bush administration passing legislations that retroactively legalized the PSP. President Obama once in office, refused to call for a full congressional investigation of the PSP. Snowden went about searching for the classified version of the report on PSP. The report he found had everything,from the complete accounting of NSA’s most secret surveillance programs and the agency directives to Department of Justice policies that have been used to support American law and contravene the US constitution. The report recorded how an NSA’s historic brief had been fundamentally altered from targeted collection of communications to “bulk collection” which is the agency’s euphemism for “mass surveillance”. It justified this shift as the legitimate corollary of expanded technological capabilities. An integral component of this plan was the program called STELLARWIND. STELLARWIND had been collecting communications since the PSP’s inception in 2001. The Bush administration attempted to legitimize it by changing the meanings of basic English words such as “acquire” and “obtain”. According to the report, it was the government’s position that the NSA could “collect” whatever communication records it wanted without having to get a warrant because it could only be said to have “acquired” or “obtained” them in the legal sense if and when the agency searched for and retrieved them for its database. This just meant that as long as American agencies were merely conducting mass surveillance, it could not be considered illegal because they were not actually “acquiring” or “obtaining” data. They were merely “collecting” it. It would be called obtaining or acquiring only when they went back into their database of collected information and pulled about a particular information. This type of word play was mindboggling.
Most people tend to think of mass surveillance in terms of “content”, i.e, the actual words in a chat or their email. But the government cares little about the actual content.Most people find it relieving but the unfortunate truth is that the actual content of our communications is rarely as revealing as its other elements, that is the metadata. Metadata is data about data. It is a cluster of tags and markers that allow data to be useful. It records all the things you do on your devices and all the things your devices do on their own. Take a phone call for example, its metadata might include the date and time of the call, the calls’ duration, the number from which the call was made, the number being called, and their locations. Metadata can tell your surveillant the address you slept last night and what time you got up this morning. It reveals every place you visited during your day and how long you spent their. It shows who you were in touch with and who was in touch with you.You do not have any control over the metadata you produce because it is generated automatically. Your devices are constantly communicating for you and they don’t withhold private information or use code words in an attempt to be discreet. Metadata is far more important than the actual content of our messages or calls or emails.
After reading the classified report Snowden spent the next weeks in a daze, he was horrified. He now understood that he was totally transparent to his government.The only two countries that had previously practiced mass surveillance were the major combatants of World War 2: Nazi Germany and Soviet Russia. The first All Union Census of the Soviet Union had a secondary agenda beyond a simple count; it overtly queried so with citizens about their nationality. Census‘s findings convinced the ethnic Russians who comprised the Soviet elite that they were the minority when compared to the aggregated masses of citizens who claimed Central Asian heritage. These findings significantly strengthened Stalin’s resolve to eradicate these cultures by re-educating their populations. The Nazi German census of 1933 took a similar statistical project but with the assistance of computer technology. It set out to count the Reich’s population in order to control it and to purge it mainly of Jews and Roma before exerting its murderous efforts on populations beyond its borders. The Reich partnered with Dehomag, a German subsidiary of the American IBM which owned the patent to the punch card tabulator, a sort of analog computer that counted holes punches into the cards. Each citizen was represented by a card and certain holes on the cards represented certain markers of identity. Soon the census information was being used to identify and deport Europe's Jewish population to the death camps.
The United States census was set up by the British monarchy as a method of assessing taxes and ascertaining the number of young men eligible for military conscription. It was the constitution’s genius to repurpose what had been a mechanism of occupation into one of democracy. The census which is officially under the jurisdiction of the Senate was ordered to be performed every 10 years which was roughly the amount of time it took to the process the data of most American censuses following the first census of 1790. This decade long lag was shortened by the census of 1890 which was the world's first census to make use of computers; the prototypes of the models that IBM later sold to Nazi Germany. With computing technology, the processing time was cut in half. It was in Japan that Snowden realized where all this technology was leading to. The ubiquity of collection was combined with the permanency of storage and any person could be selected by the government to be a scapegoat.
He was back in the United States in 2001 as an employer of Dell and attached to his old agency CIA.The title of his job was Solutions Consultant; it meant that he had to solve the problems created by his new partner who he’s going to call Cliff , the account manager. Cliff’s job was to sell Dell’s equipment and expertise to the CIA by any means and Snowden's job was to make it a reality. This meant that he had to make truth the slick promises Cliff made without any technological understanding. Their main project right now was to help the CIA catch up with the bleeding edge standards of NSA by building a private cloud. The aim was the unite the agency’s processing and storage while distributing the ways by which data could be accessed. Essentially they wanted to make it so, that someone in a tent in Afghanistan could do exactly the same work in exactly the same way as someone at CIA headquarters. The agency had a problem of having a billion buckets of data spread all over the world that they couldn’t keep track of or access so a private cloud would help people to access any data from anywhere in the world.
The realization and understanding of technological competency made Snowden even more and more paranoid. He knew every time he used his phone or his credit card he could be tracked. He recalls how once he saw at a mall a smart fridge which was being advertised as Internet equipped. It blew his mind. It had a screen, it could record audio and videos, you could check your mails, calendar, watch YouTube clips etc. Snowden was convinced that the only reason that thing was Internet equipped was so that it could report back to its manufacturer about its owners’ usage and any other household data that was obtainable. The manufacturer in turn would monetize that data by selling it. It would be another half decade before the domotics revolution, before virtual assistants like Amazon Echo and Google were welcomed into the bedroom and placed proudly on night stands to record and transmit all activity within range. The data we generate just by living would enrich private enterprise and impoverish our private existence. Corporate surveillance was turning the consumer into a product which corporations sold to other corporations,data brokers and advertisers.
Meanwhile every tech company was rolling out new civilian versions of a cloud. In fact Dell had even tried to trademark the term “cloud computing”. People were more than willing to sign up at the prospect of their data, be it photos, videos and music being universally backed up and available that they never gave much thought as to why such an uber sophisticated and convenient storage solution was being offered to them for free or so cheap.
The cloud was as effective a sales term for Dell to sell to the CIA as it was for Amzaon and Apple and Google to sell to their users. “With the cloud you will be able to push security updates across agency computers worldwide, when the cloud is up and running the agency that is the CIA will be able to track who has read what file worldwide”. The essence of cloud storage was similar to the mainframe architecture of computing’s earliest history. Now it didn’t really matter what kind of personal computer you had because the real computers that you relied upon to store your data were warehoused in the enormous data centers that cloud companies built throughout the world. To speak simply, a cloud is just a storage mechanism that ensures your data is being processed or stored not on your personal device but on a range of different servers which can ultimately be owned and operated by different companies. The result is that your data is no longer truly yours, it has become controlled by companies which can use it for virtually any purpose. When we choose to store our data online we’re often ceding our claim to it. Companies can decide what type of data they will hold for us and can willfully delete any data they object to. If any of our data is found to be objectionable they can delete our accounts , deny us our own data and yet retain a copy for their own records which they can turn over to the authorities without our knowledge or consent. Ultimately the privacy of our data depends on the ownership of our data.Our user data was returning enormous profits for the companies.
Even though certain American laws prohibit against law enforcement surveilling private citizens on their property and taking possession of their private recordings without a warrant, there are very few laws that restrain the surveillance of public property, which includes a vast majority of America’s streets and sidewalks. Law enforcement’s use of surveillance cameras on public property was promoted as a crime deterrent but soon their role became preemptive. The law enforcement started using these security cameras to track people who had not committed any crime or or even suspected of it. The greatest danger still lies ahead with the refinement of artificial intelligence capabilities such as facial and pattern recognition. An AI equipped surveillance camera would be no mere recording device but could be made into something closer to an automated police officer that filters out suspicious activities and features, such as people of a certain color or wearing certain clothes. A world in which all people were totally surveilled would be a world of equality of oppression alone. There would be no provision of leniency or forgiveness.
The constant preemptive surveillance is a way of saying that if you ever get out of line, we’ll use your private life against you.Think of a spreadsheet containing every scrap of data about you. It would pose a mortal hazard. Imagine all the secrets, big and small that could end your marriage,end your career, poison even your closest relationships and leave you broke, friendless, or maybe it’s just information about a petition you signed or a protest you attended. Everyone has something. This information was being stored by the US government.
Meanwhile,Snowden noticed that he was having strange physical symptoms. He had become weirdly clumsy falling off ladders and started feeling dizzy frequently. It led to a gradual diminishing of his senses and he couldn’t figure out if his experiences were psychosomatic or genuine. One day when he was home at around noon the dizziness hit him hard and he was sure he was going to die. He slammed into a chair and lost consciousness. After being out for around an hour he tried to reach for the phone and panic and somehow got himself downstairs and slumped on the kitchen floor and fell asleep which is how Lindsay found him. He had just had an epileptic seizure. His mother had epilepsy and it’s possible that he had gotten it from her. In time he came to know the warning signs of a seizure and he could prepare for an oncoming attack. He had his CAT scans and MRISs and other diagnoses. His brain had quite literally, short circuited.
It was May 1, 2011 when the news boomed : Osama bin Laden had been tracked down to Abbottabad in Pakistan and killed by a team of Navy SEAL. 10 years. That’s how long it had been since those two planes flew into the twin towers; what had the last decade actually accomplished? The previous ten years had been marked by a number of American made tragedies, the war in Afghanistan the catastrophy created in Iraq, indefinite detentions in Guantanamo Bay, extraordinary renditions, torture, targeted killing of civilians etc. Terrorism was the stated reason why most of the country’s surveillance programs were implemented but it turned out that Fear was the true terrorism perpetrated by a political system that was increasingly willing to use any justification to authorize the use of force. The politics of terror became more powerful than the terror itself . The repeated invocations of terror by the political class were not a response to any specific threat but a cynical attempt to turn terror into a permanent danger that required permanent vigilance enforced by an unquestionable authority. There was a permanent “us versus them”.
Due to his epileptic seizures, Snowden took a short-term disability leave from Dell. He spent his time scrolling through the news while protesters in Tunisia, Libya, Egypt, Yemen, Algeria Morocco, Iraq, Lebanon and Syria were being imprisoned and tortured by secret state agents many of which America had helped keep in power. Throughout the Middle East, innocent civilians were living under the constant threat of violence with work and school suspended, no electricity, no sewage. The crowds in the city of Cairo or be it Damascus or at every other city of the Arab Spring and Iranian green movement were calling for an end to oppression ,censorship and precarity. It was a rejection of authoritarianism, a recommitment to the humanitarian principle that an individual’s rights are inborn and inalienable.
In contemporary life we have a single concept that encompasses all space that’s off limits to the government. That concept is privacy. It is an empty zone that lies beyond the reach of the state avoid into it the law is only permitted to venture with a warrant. Because a citizenry’s freedoms are interdependent, to surrender your own privacy is really to surrender everyone’s. Saying that you don’t need any privacy because you have nothing to hide is to assume that no one should have or could have to hide anything including their immigration status, unemployment history, financial history and health records. Saying that you don’t care about privacy because you have nothing to hide is no different from saying you don’t care about freedom of speech because you have nothing to say. Or that you don’t care about freedom of press because you don't like to read. Or that you don’t care about freedom of religion because you don’t believe in God.
The young people of the Middle East were agitating for higher wages, lower prices and better pensions. They were however also agitating for a freer Internet. They were decreeing Iran’s censoring of web content and shutting down certain foreign ISP entirely. They were protesting Egypt's president who had cut off Internet access for his whole country. Snowden got up his couch and staggered over to his home office to set up a bridge relay that would bypass the Iranian Internet blockades. He then distributed its encrypted configuration identity to the Tor core developers. This was the least he could do. Even if one young kid from Iran who hadn’t been able to get online could now bypass the imposed filters and restrictions and connect to the Internet protected by the Tor system with anonymity, then it was certainly worth his own minimal efforts.The guy who started the Arab Spring was almost exactly his age. He was a produce peddler in Tunisia selling fruits and vegetables out of a cart. In protest against repeated harassment and extortion by the authorities he stood in the square and set fire to his life by dying a martyr. If burning himself to death was a last free act he could manage in defiance then, Snoowden thought, he can certainly get up off the couch and press a few buttons.
Part 3
Snowden was working at an enormous Pearl Harbor era airplane factory turned NSA facility located under a pineapple field in Hawaii. It was designed like a tunnel and hence earned its name “The Tunnel”. He was the sole employee of the aptly named “Office of Information Sharing” where he worked as a SharePoint systems administrator. SharePoint is a Microsoft product focused on internal document management, that is, who can read what, who can edit what, who can send and receive what and who can have access to what information. He was basically the reader in chief at one of the agency’s most significant facilities. He emphasizes that his active searching out of NSA abuses began not with copying of documents but with the reading of them. He was determined to find out if an American system of mass surveillance existed and if it did how it functioned.It was no easy task to correlate the various NSA’s activities; it was so secretive that by design the left hand rarely knew what the right hand was doing.
In the hopes of organizing all the documents he put together a personal best-of-the-reader- boards. The files quickly began to pile up and he realized that his personal reader board had become less of a daily digest than an archive of sensitive information with relevance far beyond the day's immediacy. He decided to share it with others in the agency who would do good reading about the department they were working at. So with his bosses’ approval he set about creating an automatic reader board, one that did not rely on anybody posting things to it but edited itself. The reader board essentially scanned for new documents and its findings would be made available to every NSA officer by comparing their digital identity badges and documents pertaining to their relevance would be sent to them. Essentially it would be a reader board of individually tailored news feed. He called the system Heartbeat. Nearly all of the documents that he later disclosed to journalists came to him through Heartbeat. It showed him not just the aims but the abilities of NSA’s mass surveillance. Snowden explains NSA’s surveillance as a matter of six protocols: sniff it all, know it all, collect it all, process it all, exploit it all, partner it all. It intended to impress America’s allies Australia,Canada, NZ and the UK:the primary countries with which the United States shared intelligence. Together with the United States these countries are known as the Five Eyes. Sniff it all meant finding a data source, Know it all meant finding out what the data was, Collect it all meant capturing that data, Process it all meant analyzing that data for usable intelligence and Exploit it all meant using that intelligence to further the agencies aims and Partner it all meant sharing the new data source with allies.
He found an order from the FISA code demanding a private company to turn over its customers’ private information to the federal government The NSA had secretly interpreted this authorization as a license to collect all of the business records or metadata of telephone communications coming through American telecom such as Verizon and AT&T on an ongoing daily basis of each and every customer. This included records of telephone communications between American citizens the practice of which was unconstitutional. This legalization was being used to justify two most prominent Internet surveillance methods: the PRISM program and upstream collection. PRISM enabled the NSA to routinely collect data from Microsoft, Yahoo, Google, Facebook, Paltalk, YouTube,Skype, Apple and AOL including email, photos, video and audio chats, web browsing content and all other data stored on clouds. Upstream collection meanwhile was arguably even more invasive and enabled the routine capturing of data directly from private sector internet infrastructure. This collection was managed by NSA’s special sources operations unit which built secret wiretapping equipment and embedded it inside corporate facilities of obliging Internet service providers around the world.
The next stage of his investigation was to figure out how this collection was actually accomplished. Imagine you’re sitting at a web browser and you type in a URL which is a request that goes out in search of his destination server. Somewhere in the midst of its travel before your request gets to that server it will have to pass through TURBULENCE, one of NSA’s most powerful weapons. Your request passes through a few black servers in special rooms at major private telecommunication buildings throughout allied countries as well as in US embassies, and contain two critical tools. The 1st :The program called TURMOIL handles passive data collection, making a copy of the data coming through. The 2nd program: TURBINE, is in charge of active collection that is actively tampering with the users. Seeing a request, it checks the metadata for selectors for more scrutiny. If TURMOIL flags your traffic as suspicious, it tips it over to TURBINE which diverts your request to the NSA’s servers. Their algorithms decide which of the agency’s exploit-malware programs to use against you. These chosen malware are sent back to TURBINE which injects them into the traffic channel and delivers them to you along with the website you requested. The end result is that you get all the content you want along with all the surveillance you don’t and it all happens in less than 686 milliseconds. NSA can access not just your metadata but your data as well. Your entire digital life now belongs to them.
The NSA does not regard citizens data as their legally protected personal property. The NSA maintains that because citizens had already shared their phone records with a third party that is your telephone service provider, they had forfeited any constitutional privacy interest they may once have had. In early 2013 James Clapper, director of national intelligence testified under oath to the US Senate that the NSA did not collect any type of data at all on millions or hundreds of millions of Americans. This was a bald faced lie. When civil society groups like ACLU try to challenge NSA, the latter did not defend itself and instead declared that ACLU had no right to be in court at all and that existence or nonexistence of surveillance was a state secret. In other words the court couldn’t recognize the information that was publicly known from having been published in the media, it could only recognize the information that the government officially confirmed as being publicly known.
Leaking and whistleblowing isn’t the same thing. Leaking is disclosure done not out of public interest but out of self interest when someone may leak a confidential information for some money or out of spite. The agency itself leaks some documents for its own benefit such as the leaking of detailed accounts of a conference call between al Qaeda leader Ayman Al Zawhiri and his global affiliates helped the agency to inflate the threat of terrorism and deflect criticism of mass surveillance. Whistle blowing on the other hand is an act in which a person who through hard experience has concluded that their life inside an institution has become incompatible with the principles developed in the greater society outside it to which that institution should be accountable. Whistle blowing is not a radical act of dissent or resistance but a conventional act of return to original principles.Snowden decided to become a whistleblower.
He started planning how he would reveal top secret documents to the public. Cooperating with some type of media organization would defend him against the worst accusations of a rogue activity but the lack of journalists’ expertise and technology made him question his decision. He says that the journalists have failed to pick up on two events that stunned him. The first was NSA announcement of the construction of a vast new data facility called Massive Data Repository. No one bothered to ask why any government agency let alone an intelligence agency needs that much space for data storage? What data and how much of it? The next event happened one year later in March 2013 after Clapper denied that NSA collected bulk data on Americans. But no one covered a rare public appearance by Ira Hunt , the chief technology officer of CIA. He was appearing as a special guest speaker at a civilian tech event in New York called the GigaOm structure data conference. At the conference he said that, “At the CIA we fundamentally tried to collect everything and hang onto it. It is nearly within our grass to compute on all human generated information”. He told the journalist that, “the agency could track their smartphones even when they were turned off and they could surveil every single one of their communications”. Coverage of Ira’s confession ran only on Huffington Post but the performance itself ran live on at YouTube where it still remains.
Meanwhile the CIA had finally decided on the disposition of its cloud contract with Dell and had turned down HP too. They instead signed a 10 year deal of 600 million dollar cloud development and management with Amazon.
Snowden finally narrowed down on documentarian Laura Poitras to reveal NSA’s documents. Her film “My Country, My Country” depicted the 2005 Iraqi national elections that were conducted under US occupation. She had also made the program about NSA cryptanalyst William Binney. Laura herself had been frequently harassed by the government because of her work. Glenn Greenwald was a civil liberties lawyer turned communist who wrote about the unclassified version of the NSA IC report back in 2009 . The problem was how to get in touch. He used the alias “cincinnatus'' which was followed by “citizen 4”. Anonymity was very important in order to avoid being tracked by the CIA. He decided to use somebody else's Internet connection. He couldn’t use public Wi-Fi because it leaves on record with every access point it connects to. So he went driving. He converted his car into a roving Wi-Fi sensor for which he needed a laptop, a high powered antenna and a magnetic GPS sensor. He took along a cheap laptop working on Linux based “amnesiac” operating system meaning, it forgets everything once you turn it off. At night and on weekends he drove around for hours letting his antenna pick up the pulses of each Wi-Fi network he passed and his GPS sensor tagged each access point with the location at which it was noticed. What resulted was a map of invisible networks we pass by every day without even noticing, many of which had no security or very little security. Thus he tried to get in touch with the journalists who would be willing to expose the documents to public.
“Read, Write, Execute” was his simple three step plan. Almost everything we do on a computer or any device leaves a record. Each permission he used left its own forensic trace; every time he opened a file, copied, downloaded, moved, or deleted, everything was recorded. Luckily the strength of the systems were also their weaknesses; their complexity meant that not even the people running them necessarily knew how they worked. The NSA may have paid for the network but sysadmins like Snowden were the ones who really owned it. The Read phase would involve dancing through the digital grid of tripwires laid across the routes connecting the NSA to every other intelligence agency domestic and foreign. One such program was OPTICNERVE approach that saved a snapshot every five minutes from the cameras of people video chatting on platforms like Yahoo or Messenger. By using HEARTBEAT to bring in the documents he wanted he could award suspicion. He could just say he’s compiling documents for the reader board that everyone knew about. Now, he couldn’t just copy the files from HEARTBEAT server onto a personal storage device without being caught. If you try to transfer files from the server he could easily be tracked, so he decided to make use of some old computers lying around in the NSA facility which were not connected to the central network. If anyone asked, he could say that he was making sure HEARTBEAT was compatible even on old computers since not everybody has sophisticated technology experience. Under the guise of compatibility testing he could transfer the files to these old computers where he searched, filtered and organized them as much as he wanted. The WRITE phase now included copying the documents from these old computers into SD cards. The process was excruciatingly slow considering the amount of documents that were to be copied and by the end of the process he would be so paranoid he’d be sweating, seeing shadows and hearing footsteps around every corner.
Execute was the final step. He had to get that vital archive of documents out of the building. After sneaking out the SD drives from the facility he had to transfer the files to a larger external storage device via his laptop. Now the problem of anonymity arose. He knew that the documents could lead back to him once he had sent them to the journalists because all digital files contain metadata, invisible tags that can be used to identify the origin. He thought of stripping the metadata but that could cast a doubt on their authenticity. And even if you strip the metadata, there was no guarantee that the documents had not been embedded with further unique identifying programs that could track the sender of information. This technological difficulty forced him to confront the prospect of discarding his practice of anonymity and coming forward to identifying himself as the source. He decided to embrace his principles by signing his name to them and letting himself be condemned. All the documents he selected fit on a single drive which he left out in the open on the desk at home. He knew that the materials were just as secure as they had been at office, actually more , thanks to multiple levels and methods of encryption he had covered them in. That’s the beauty of cryptological art. A little bit of math can keep a secret.
Most people think that apart from read, write and execute there is another basic function called delete. What does deleting mean? As countless despots have been reminded, to truly get rid of a document you can’t just destroy every copy of it. You also have to destroy every memory of it which is to say you have to destroy all the people who remember it. Deleting functions appeared from the very start of digital computing so that users could feel in control of their mistakes. But the truth is that deletion has never existed technologically in the way we conceive of it. The file only appears to be deleted.Deletion is a public fiction, a lie. In technical terms deletion is really just a form of overwriting. Normally when we press delete for one of our files, its data which has been stashed deep down on a disk somewhere is not actually touched. Only the computers map of where each file is stored is rewritten to say that the space where the file belong is now empty. A good analogy would be to think of a book in a vast library that is not mentioned in the records of the library. Just the fact that it is not named in library references does not mean that the book does not exist. Similarly, the deleted file remains stashed deep inside our device, and we look really really close, we can still find it.This is why it takes so long to copy a file but the act of deletion is almost instantaneous.
In 2012, the governments of both Australia and UK were proposing legislation for the mandatory recording of telephone and Internet metadata. These were presented as public safety measures but they actually represented a breathtaking intrusion into the daily lives of the innocent. Sometime during the year Snowden attended a gathering called a crypto party in Honolulu where international grassroots cryptologists volunteer their time to teach free classes on the topic of digital self defense. Snowden started his presentation by explaining the illusory nature of deletion. Then he pivoted to encryption. It is the only true protection against surveillance. If all the emails in your inbox are encrypted Google can’t read them to profile you unless it has the encryption key. If all your communications are encrypted, spies can’t read them unless they have the encryption key. Encryption works by way of algorithm. As a mathematical method of reversibly transforming information in a way that it becomes incomprehensible to anyone who doesn't have a copy of the encryption key. Encryption algorithms are basically just sets of math problems designed to be incredibly difficult even for computers to solve. The encryption key is the one clue that allows a computer to solve the particular set of math problems being used. Your readable data is pushed into one end of the encryption algorithm and it gives out incomprehensible gibberish called ciphertext. If anybody wants to crack the ciphertext they must have the encryption key. The security of an encryption key is based on its length which indicates the level of difficulty involved in solving the algorithm.If you presume that an attacker takes one day to crack a 64 bit key which scrambles your data in one of 2^64 possible ways, then it would take double that amount of time, two days to break a 65 bit key and four days to break a 66 bit key. Breaking a 128 bit key would take 2^64 times longer than a day, or 50,000,000 billion years. In his communications with the journalists, Snowden used 4096 and 8192 bit keys. Even all of NSA’s cryptoanalysts using all of the world’s computing power put together would not be able to get into his drive. For this reason encryption is the single best hope for fighting surveillance of any kind. Any government hoping to access encrypted communication has two options, go after the key Masters or go after the keys. For the former they can pressure device manufacturers into intentionally selling products that perform faulty encryption. For the latter they can launch targeted attacks against the endpoints of the communication that is the hardware and software that perform the process of encryption. The best means we have for keeping our keys safe is called Zero knowledge. It is a method in which any data you try to store externally on a cloud, is encrypted by an algorithm running on your device before it is uploaded and the key is never shared. In the zero knowledge scheme, the keys are only in the user’s hands and no one can touch them. Snowden’s key to the NSA secrets went beyond zero knowledge, it was a zero knowledge key consisting of multiple zero knowledge keys. The keys to the drive containing the disclosures had a twist. While he distributed most of the pieces of the keys, he retained one for himself. If you destroy just the single lone piece that he kept for himself he would destroy all access to the NSA’s secrets forever.
Snowden wanted to find out if there was anyone in the world the NSA could not surveil. The program that enabled the robust access to individuals was called XKEYSCORE which was a sort of search engine that let an analyst search through all records of your life. A kind of Google that instead of showing pages from public Internet returns results from your private email or private chats, your private files, everything. Snowden applied for the job of infrastructure analyst which involved using the complete spectrum of NSA’s mass surveillance tools including XKEYSCORE to monitor activity on the infrastructure of interest, that is, the Internet. He decided to bring out archives of the agency and pass them through the journalists he had contacted. The NSA described XKEYSCORE in the documents as its widest ranging tool used to search nearly everything a user does on the Internet. It was the closest thing to science fiction he had ever read, the difference being that this was a science fact. The interface allowed you to type in pretty much anyone’s address, telephone number and go through the recent history of their online activity. You could even playback recordings of their online session so that the screen you would be looking at, was the screen whatever was on the user’s desktop. You could read their emails, their browser history, their search history, everything. You could set up notifications that would pop when they became active on the Internet.
Sometimes this elaborate software was used by analyst to stalk their love affairs or their partners and to hack into their phones and chats. Or other times he learned that intercepted nudes were a kind of informal office currency; an analyst would share the nudes they had acquired of random strangers with colleagues. Right there sitting at his screen Snowden had access to almost every single human that had ever used a computer or had been on the Internet.
He thought to himself, “I’ll never see my family again”.
He started making preparations like those of a man who was about to die. He emptied his bank accounts putting cash into an old steel ammo box for Lindsey to find. He started doing his procrastinated chores and encrypted his old computers . In sum, he was putting his affairs in order to make everything easier for Lindsey or just for his conscience which was about to switch allegiance from a world that hadn't earned it to the woman who had and the family he loved. It was difficult to get the journalist to come to a meeting because he couldn’t tell them who they were meeting. It was even more difficult to find a place where he could meet them. All of the Five Eyes countries were obviously off limits. In fact all of Europe was out because these countries couldn’t be counted upon to uphold international law against the extradition of those charged with political crimes in the face of what was sure to be significant American pressure. Africa, Latin America were no go zones too. The United States had a history of acting there with impunity. Russia was out because it was Russia and China was China. The optics would only be worse in Middle East. It seemed like no when he was independent enough from the White House. The process of elimination left him with Hong Kong, sort of a nomansland but with a vibrant media and protest culture and a largely unfiltered Internet. That night he lay in bed and held Lindsey too tightly. He told her he was sorry and how busy he had been; he said he was going to miss her and she was the best person he had ever met in his life. After Lindsay left for a trip with her friends Snowden broke down and started crying. He took an emergency medical leave from work citing epilepsy, packed his luggage for laptops, secure communications and a computer that had never gone and would never go online etc. He left his smartphone on the kitchen and alongside her notepad scribbled, “Got called away for work, I love you”. Then he went to the airport and bought a ticket to Tokyo. In Tokyo he bought another ticket in cash for Hong Kong, the city where world first met Edward Snowden.
A single mistake would have been enough to get him caught by the NSA. He had imagined all sorts of unpleasant scenarios. He barricaded himself in the room at Mira hotel and didn't leave his room for days out of paranoia. Finally Laura and Glenn showed up in Hong Kong on June 2. They seem to be disappointed looking at him as they expected someone older, tipsy, depressive man with a guilty conscience waiting to expose the NSA. In the room Laura started rearranging and adjusting the lights and setting up her camera. They talked and talked about the ongoing NSA’s programs while Laura filmed. Glennan and Evan would retreat to their own hotels to write up their findings into an articles while Laura would edit her footage and do her own reporting with Bart Gilman of Washington post. On June 5, the Guardian broke the first story of the FISA court order that authorized the NSA to collect information from the American telecom Verizon about every phone call it handled. On June 6, it ran the PRISM story pretty much simultaneously with a similar account in the Washington post by Laura Ann Bart. Snowden knew he would soon be identified. As the revelations ran on every news channel, it became clear the US government had thrown the whole of its machinery into identifying the source. He had to seize the initiative before it was too late and the US government gave it a different spin. He had to come forward and identify himself. Laura proposed a recorded statement which she started filming right then and there most of which has been included in her documentary Citizen 4. Snowden faced the camera and said, “My name is Ed Snowden. I am 29 years old”.
Hello world.
All he cared about was getting the facts out into the world. He was at the public’s mercy. The major impedance to justice was a major flaw in the law, a purposeful flaw created by the government. Someone in his position would not be allowed to argue in a court that their disclosures were beneficial to the public. The only thing the court would recognize was that he disclosed classified information to journalists which was supposed to be state secrets. Laura’s video of him was posted on Guardian website on June 9. He knew how the stories of several other whistleblowers had gone like Daniel Ellsberg, Anthony Russo, Thomas Tam, Drake, Benny, Loomis etc all of these people had faced some sort of backlash.
Within hours after his Guardian video ran, one of Glenn’s regular readers in Hong Kong contacted him and offered to put him in touch with Robert Tibbo and Jonathan Mann to local attorneys who then volunteered to take on his case. They helped him get out of Mira hotel and took him to one of the poorest neighbors of the city to help him hide. He was supposed to live with refugees who offered him there home with unfailing kindness and grace. All of these people were asylum seekers and he remains on good terms with them even today.
With the US government having decided to charge Snowden under Espionage Act, he stood accused of a political crime, meaning a crime whose victim is the state itself, than a person. The team supporting him had reached out to officials everywhere from Iceland to India asking if they would respect the prohibition against extradition of those accused of political crimes. It soon became evident that even the most advanced democracies were afraid of incurring the wrath of the US government. Enter Sarah Harrison, a journalist and editor for WikiLeaks who was poised to offer him the world’s best asylum advice. She made a plan to travel to Quito, Ecuador, via Moscow via Havana via karikas for a simple reason it was the only safe route available. There were no direct flights to Quito from Hong Kong and all of the other connecting flights travel through US airspace. They landed at Moscow airport on June 23 for a 24 hour layover till the next flight. It has now dragged on for over 7 years. Exile is an endless layover.
As he got in line for the customs, two security officers in suits approached and said there is a problem with the passport. They took him to a conference room with men in grey sitting around a table where there were a half dozen of them with military haircuts. It was Russia’s FBI, the Federal Security Service. In very polite terms and decent English this spoke to him the gist of which was “come and work for us”. And return for cooperation they were offering him anything from stacks of cash to a get out of jail free card, for pretty much anything, from fraud to murder. Snowden said, “Listen I understand who you are please let me be clear that I have no intention to cooperate with you. I’m not going to cooperate with any intelligence service”. He informed that he was going to Quito, Ecuador via Havana. The men informed him, “I’m afraid to inform you that your passport is invalid your passport has been canceled by your government and the air services have been instructed not to allow you to travel”. It was incredulous! His own government had trapped him in Russia. When you’re trying to catch a fugitive, putting out an Interpol alert and canceling their passport is just standard operating procedure. But in the final accounting it was served as a defeat, as it handed Russia a massive propaganda victory.
All told, they were trapped in the airport for a biblical 40 days and 40 nights. Over the course he applied to a total of 27 countries for political asylum and all of them denied. Soon his presence became a global spectacle, even the Russians found it a nuisance. On July 1, the president of Bolivia, Eva Morales left another airport in Moscow in a Bolivian state plane. The US government suspected that he was on board due to president Morale’s expression of solidarity and pressured the governments of Italy,France and Spain and Portugal to deny the plane access to their airspace and succeeded in diverting it to Vienna, Austria. This was a startling violation of Russian sovereignty. The incident wasn’t affront to Russia which couldn’t guarantee a visiting head of state safe passage home. And it confirmed Russia and to him that any flight that America suspected him of stowing away on, ran the same risk of being diverted and grounded. On August 1, Russia granted him temporary asylum.
This part of the book takes entries from the Diaries of Lindsay Mills. Snowden says that ever since he left home he had no idea what had been going on with his family and the best person to tell would be no other than Lindsay herself. The following account is in Lindsey’s own words from her personal journal.
Lindsey writes that Edwards mother was to come over at his invitation on 22nd may but he was not at home when she woke up. She checked her phone and found three missed calls from an unknown number and one missed call from along for a number no voice mails. She googled the long number. Ed must be in Hong Kong for some work. On 24th may she started getting worried, “Where is Edward?”. On June 7, she received a call from NSA special agent Megan Smith asking her to call him about Ed. She was being followed by government agents and SUVs. Some HPD officers searched through the house and over the next few days she was followed by government vehicles wherever she went. On 9th June, a friend called Tiffany called her and asked her to watch the news. She turned on the news and waited for the 12 minute YouTube video to load. And then there he was, real, alive. He looked thin but he sounded like his old self. The old Ed,confident and strong. This was the man she loved, not the distant, cold ghost she had been recently living with. She thought, “Ed what have you done? How can you come back from this?”
Her friends helped her through the constant interrogations, interviews and searches; her name was all over the media: Lindsay Mills, the girlfriend of Edward Snowden. She took care of all her affairs with urgency like withdrawing all her money kept at banks in case the government froze her accounts. She hired some lawyers to represent her. The interviewers asked her question with the complacency that showed that they already knew everything about her. That was Ed’s point. The government always knows everything.
The next few days were marred with exhausting interrogations again and again, she was frustrated. The feds had copied all of her emails and chats and printed out and read things that she had written to Ed and that Ed wrote back to her, demanding that she explain them. But this is just how people who have been together for eight years communicate! Agents even followed her around the women’s department. The Internet and TV was full of labels calling her a stripper or a whore.
She finally understood why Edward had insisted on calling her mother. They would be together. He had wanted them to be together in Hawaii when he went public so that they could keep each other company and give each other strength and comfort. It’s so hard to be angry at someone you love and even harder to be angry at someone you love and respect for doing the right thing. She decided to move to LA and started packing her stuff like a crazy woman and cleaning up and then just gazing at his side of the bed. All that was left of Edward stuff after the FBI raided the house fit into one small box; she set it alight with a box of matches and just watched it burn.
Love and exile:
Once American spy agencies had proven to themselves that it was possible to passively collect all your communications, they started actively tampering with it too. Now they were capable of winning total control of your whole device including his camera and microphone. Which means that if you are reading this book on any sort of modern machine like a smartphone or tablet they can follow along and read you. They can tell you how quickly or slowly you turn the pages and whether you read the chapters consecutively or skip around. This is a result of two decades of unchecked innovation, the final product of a political and professional class that dreams itself your master. The revelations of 2013 particularly roused Congress, both houses of which launched multiple investigations into NSA abuses. Those investigations concluded that the agency had repeatedly lied regarding the nature of its mass surveillance programs. In 2015, Court of Appeals ruled in the matter of ACLU versus Clapper.The court ruled that an NSA program had violated even the new standards of the Patriot Act and was most probably unconstitutional. In the court’s opinion the government’s definition of “relevant data collection” was so expansive as to be virtually meaningless. The amount of data they collected was unprecedented and unwarranted. Snowden says that the American legal resistance to mass surveillance was just a beta phase of what has to be an international opposition movement fully implemented across both governments and private sector. The reaction of technocapitalists to the disclosure was immediate and forceful. The documents revealed NSA so determined to pursue all information it perceived as being deliberately kept from it, that it had undermined the basic encryption protocols of the Internet, hence making citizens financial and medical records for example more vulnerable. Eventually, Apple adopted strong default encryption for its iPhones and iPads and Google followed suit for Android products and Chromebooks. But perhaps the most important private sector change occurred when businesses throughout the world set about switching their website platforms replacing HTTP with the encrypted HTTPS; the “S” signifies Security, which helps prevent third party interception of web traffic. The year 2016 was a landmark in tech history. The Internet is certainly more secure now than it was in 2013. Snowden now works for his Freedom of Press foundation, a nonprofit organization dedicated to protecting and empowering public interest journalism in the new Millennium. To that end the FPL financially supports Signal, an encrypted texting and calling platform created by open whisper systems, and developed Securedrop originally coded by the late Aaron Swartz, an open source submission system that allows media organisations to securely accept documents from anonymous whistleblowers.
Internationally the disclosures had to revive debates about surveillance in places with long histories of abuses. The countries whose citizens were the most opposed to American mass surveillance were those whose governments had most cooperated with it, from the Five Eyes nations. Specially the citizens of Germany who to learned that the NSA was surveilling German communications and had even targeted Chancellor Angela Merkel’s smartphone. Nearly every country in the world found itself in a similar bind” its citizens outraged, its government complicit. For the first time since the end of World War 2, liberal democratic governments throughout the world were discussing privacy as the natural inborn right of every man, woman and child. The EU established a new directive that seeks to standardize whistleblower protection across its member states along with a standardized legal framework for privacy protection. The GDPR treats the citizens of European unions as “data subjects”, that is, people who generate personally identifiable data. In the US data is usually regarded as a property of whoever collects it. But the EU posits data as a property of the person it represents which allows it to treat our data subject as deserving of civil liberties protections. The GDPR is undoubtedly a major legal advance but even its transnationalism is too parochial The Internet is global. Our data wanders far and wide. Our data wanders endlessly. We start generating this data even before we are born when technologies detect us in the utro and data will continue to proliferate even after we die.This is why we have a special duty; we must ensure that these records of our past can’t be turned against us or turned against our children.
We must make sure that the world we leave behind for our children should be free of this pressure of mass surveillance. If you don’t actually claim our data now our children might not be able to do so. Our data is used for algorithms to analyze it for patterns of established behavior in order to extrapolate behaviors to come, a type of digital prophecy that’s only slightly more accurate than analog methods like palm reading. We can’t allow ourselves to be used in this way, to be used against the future. We can’t permit our data to be used to sell as the very things that must not be sold such as journalism. We can’t let the God like surveillance we’re under be used to calculate a citizenship scores or to predict our criminal activities to tell us what kind of education we can have or what kind of job we can have to discriminate against us based on our financial legal and medical histories not to mention our ethnicity or race which are constructs that data often assumes or imposes. Of course all of the above has already happened and it’s still happening.
Exile: When people ask Snowden what his life is like now he tends to answer that its a lot like there’s, in which he spends a lot of time in front of the computer reading, writing and interacting. He lives in a 2 bedroom apartment in Moscow and attends several conferences on the protection of civil liberties in the digital age to audiences of students, scholars, lawmakers and technologists. He has virtual meetings with fellow board members at the Freedom of Press foundation. On other days he just picks up some Burger King. That was his life which got significantly brighter during the freezing winter of 2014 when Lindsay came to visit him, the first time he had seen her since Hawaii. He knew he did not deserve the chance. When she opened the door and saw him, she placed her hand on his cheek and he told her he loved her. “I know” she said. They held each other in silence each breath like a pledge to make up for lost time. From that moment his world was hers. Lindsay forced him to get out of his room and go sightseeing which he had never done in those years alone. She helped him calm down his paranoia. Whenever he goes outside he tries to change his appearance a bit, maybe get rid of his beard or wear different glasses just for the semblance of some anonymity. He changes the rhythm and pace of his work and looks away from traffic when crossing the street. He used to worry about the bus and Metro but nowadays everybody is too busy staring at their phones to give him a second glance. Lindsay’s russian has grown to be better than his own. She also laughs more easily and is more patient and generous and kind. Lindsay moved out to be with him three years ago and two years ago today they got married.
(Update: Lindsay and Edward gave birth to a baby boy in December 2020.)
Concluding, in the words of Edward Snowden, “The only way I can end this book is the way I began it, with a dedication to Lindsay, whose love makes life out of exile”.
fin.
-----------------------------------------------------------------------------------------------------------------------
REVIEW: okay, firstly, MASSIVE impressed with Edward Snowden’s writing style. He is an excellent storyteller. Absolutely in love with Lindsay and him and their story. This is book that has no criticism. Snowden revealed some of the biggest state secrets with grave threat to his life that everyone needs to read upon. He stresses on the need to understand technology that has surrounded our lives which I think is SO important. If you’d like to read more about the revelations that Edward Snowden made, you can check them out here.
Fun fact: Snowden only follows one account on Twitter. No it’s not his wife. It’s the NSA. LMFAOOO T_T
oK DAS IT.Drop comments pls. Im exhaUSTED.
------------------------------------------------------------------------------------------------------
Hey everyone,
I hope you liked the book. Pleased drop your comments below!!
If you’d like to support me in any way or show appreciation, you can find ways to do so in my linktree. Your voluntary support helps me to keep the letter free and accessible to all.
Thankyou! <3
Hanan.


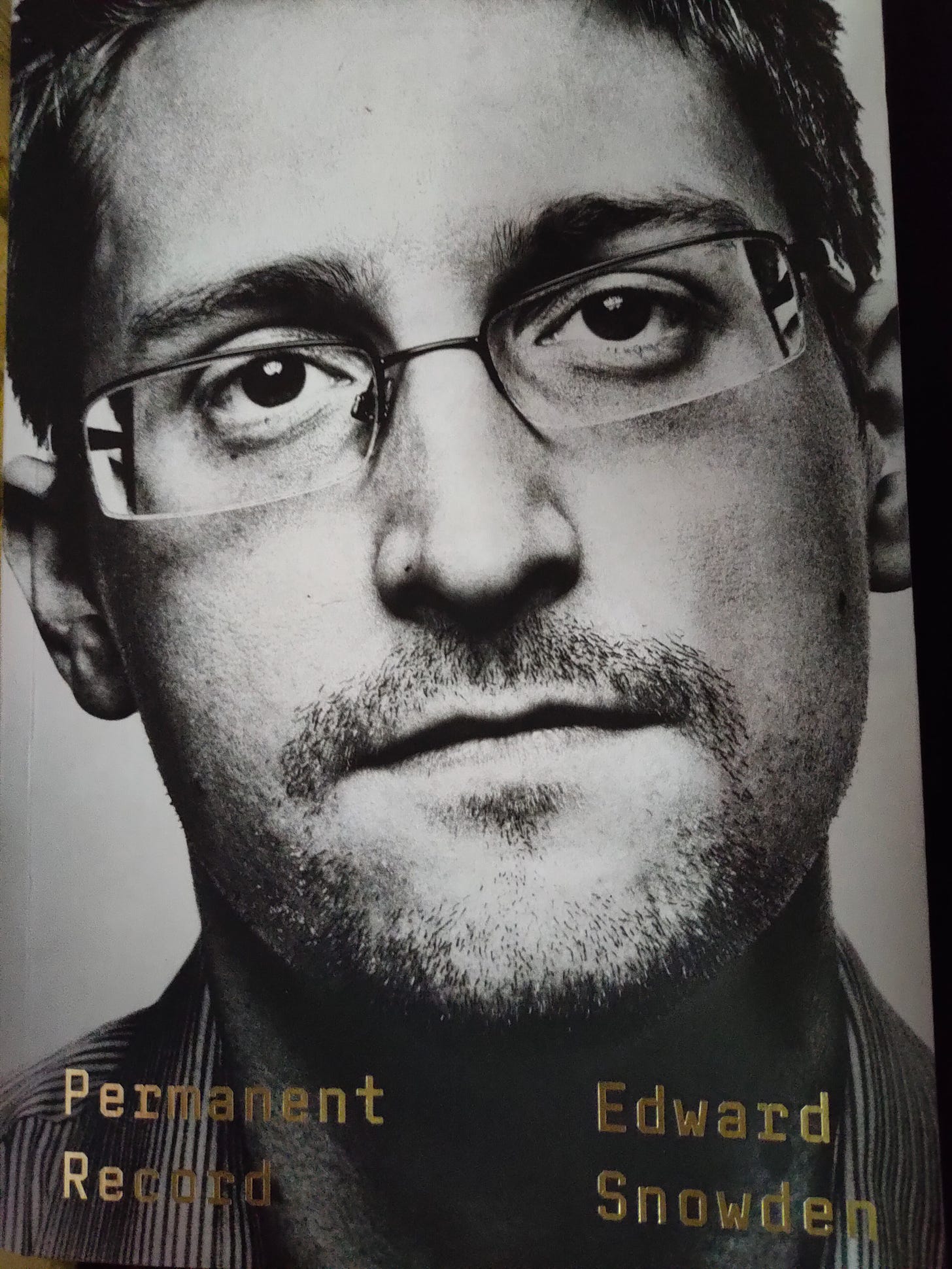
oh boiii....That was mind-blowing and feels like it is much more intricate than I thought it was. Also cant even imagine how it feels to live like Ed and Lindsay. Thanks Hanan <3
Great review, Hanan! Thanks again for reading for all of us!